The digital world is facing an ongoing development of new online fraud schemes which include the advanced phishing method known as Phishing 2.0. The scams have evolved from their initial fake email system to their current use of advanced techniques which include AI-created content and authentic-looking websites and their three-part deception system. The majority of users will not perceive anything out of the ordinary during the initial stage. Your financial security can be protected through daily internet activities when you learn about the latest security methods and their detection methods.
AI-Generated Scam Messages Are Rising
Scammers now use AI tools to create realistic emails and messages. Reports indicate that more than 60 percent of phishing attacks currently use AI-generated materials which make their detection more difficult.
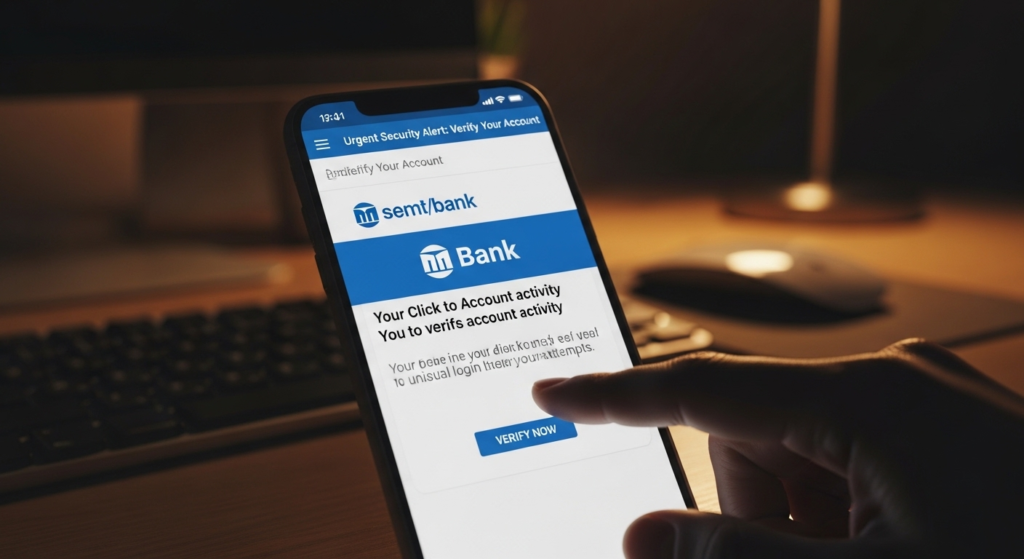
Multi-Channel Attacks Are Increasing

Phishing attacks now extend beyond their traditional email delivery method. Attackers use SMS, social media, and messaging apps together. Studies show that more than 70% of cyber attacks now use multiple attack methods across different platforms.
Fake Websites Look Almost Real
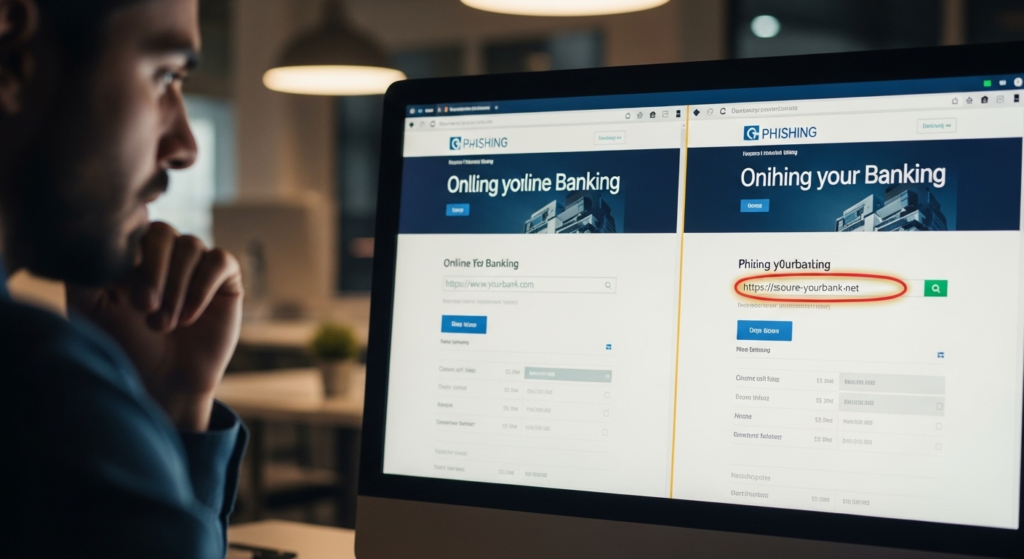
Modern phishing sites closely copy real banking or shopping websites. Even experienced users may find it difficult to spot small differences in links or design.
QR Code Phishing

QR code scams are growing globally. Users scan codes which direct them to fraudulent login websites. Reports indicate a significant rise in QR-based phishing activities during the past few years.
Personalized Targeting

Scammers collect personal data from social media to create targeted messages. This method increases success rates as messages feel more relevant and trustworthy.
Deepfake Voice and Video Scams

It would not be wrong to say that some attackers use AI-generated voice or video to impersonate trusted people. This technique adds a new layer of realism to financial scams.
Cloud and App-Based Phishing

Fake login pages for cloud services and apps have become a widespread problem. The attackers use various methods to obtain login credentials which they will use to access bank accounts.
Small Test Transactions First

Attackers begin their testing process by using small transactions to check their ability to access systems. This process allows them to verify their system access before proceeding to conduct bigger operations.
Delayed Detection of Fraud

Many users notice scams only after checking statements. The reports show that most victims discover fraud after several hours or days which makes the consequences more severe.
Global Financial Impact Is Growing

Finally, Cybercrime reports estimate that phishing-related losses reach billions of dollars globally each year showing the scale and impact of these attacks. Be smart and informed about these things to save yourself and your families.
